Mandjur
Mandjur has been running their business for more than 100 years. Since 1918, they managed to effectively provide traditional and herbal medicine for their customers in Indonesia. They need someone with deep knowledge in Magento for deep technical bugs that they might have. They chose to maintain their site on hourly contract.
Challenge
1. Speed Optimizations
2. Recovering from an unknown attack
3. Fixing Security issues
4. Adding Google Custom Search Engine
5. Midtrans Integrations
6. General Maintenance
Solution
1. When they’re moving to us, the server load speed (or Time To First Byte) was extremely bad for them. The website is sluggish. We do an audit and draw a conclusion it’s from the network speed. This is because a ‘curl’ from the server to outside images, are extremely slow, which indicates the server is terrible. Mandjur owns their own dedicated server, so this is pretty weird. As it turns out, Mandjur.co.id is using this ‘promotional’ server co-location that was offered by the sales person for a ‘big discount’. The big discount actually comes with moving the Mandjur server in a new location within their data center that is not yet optimized. The client actually has to go to the hosting office to move the Mandjur server physically back to the proper data center.

2. Mandjur site got defaced:
- We actually identified that the hacker attacked Mandjur by changing its index.php and wipe out some files in this directory js/mage/adminhtml/product/composite/. But we successfully got the files back.
- We identified this by using our custom malicious file scanner to scan through the entire code base and automatically flag any malicious files.
- We then removed those codes, and recovered them.
- Up next, we need to fix security issues that are in Mandjur.
- Why does this happen? Mandjur still uses Magento 1.7 which is a very old distributions, the source is also never patched.
- 3. Next is fixing security issues
- We apply security patches to the code base.
- We reviewed and removed all unused user accounts on the server.
- We reset the root password of the server, mysql database.
- We assign the code to a custom owner so if an attacker manages to change the core code, the attack is localized only on that code instead of root user where the attacker can change anything on the server.
- We update all Magento admin panel passwords.
- We use a Magento attacker client to try out attacking the server. Since the attack doesn’t happen again. We close this issue.
- Assign default permissions to all code files.
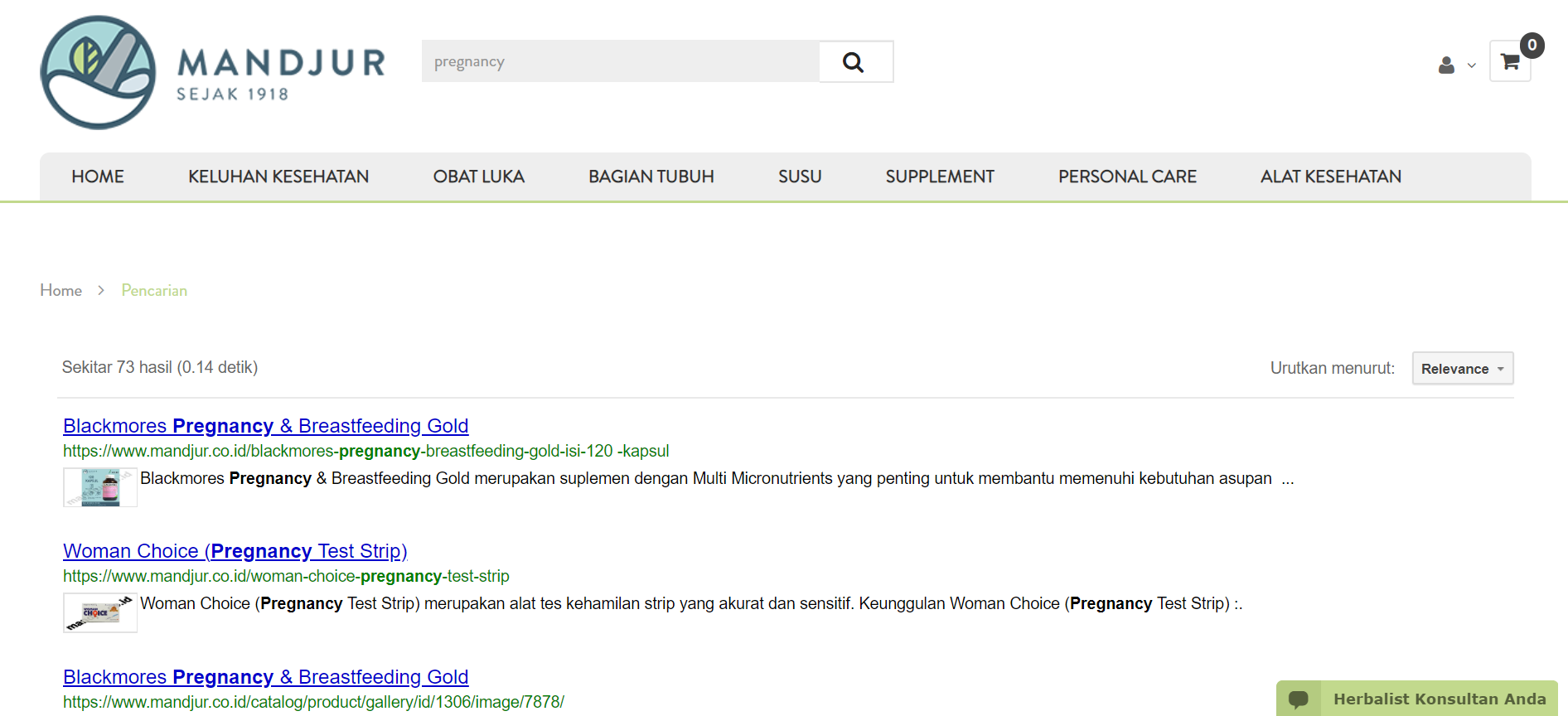
- 4. Since we knew using a third-party module would cost more money to our client, we made our own static-block to develop this search feature for the website. Our self-developed Google Custom Search Engine will give the customer the search result way faster and more accurately
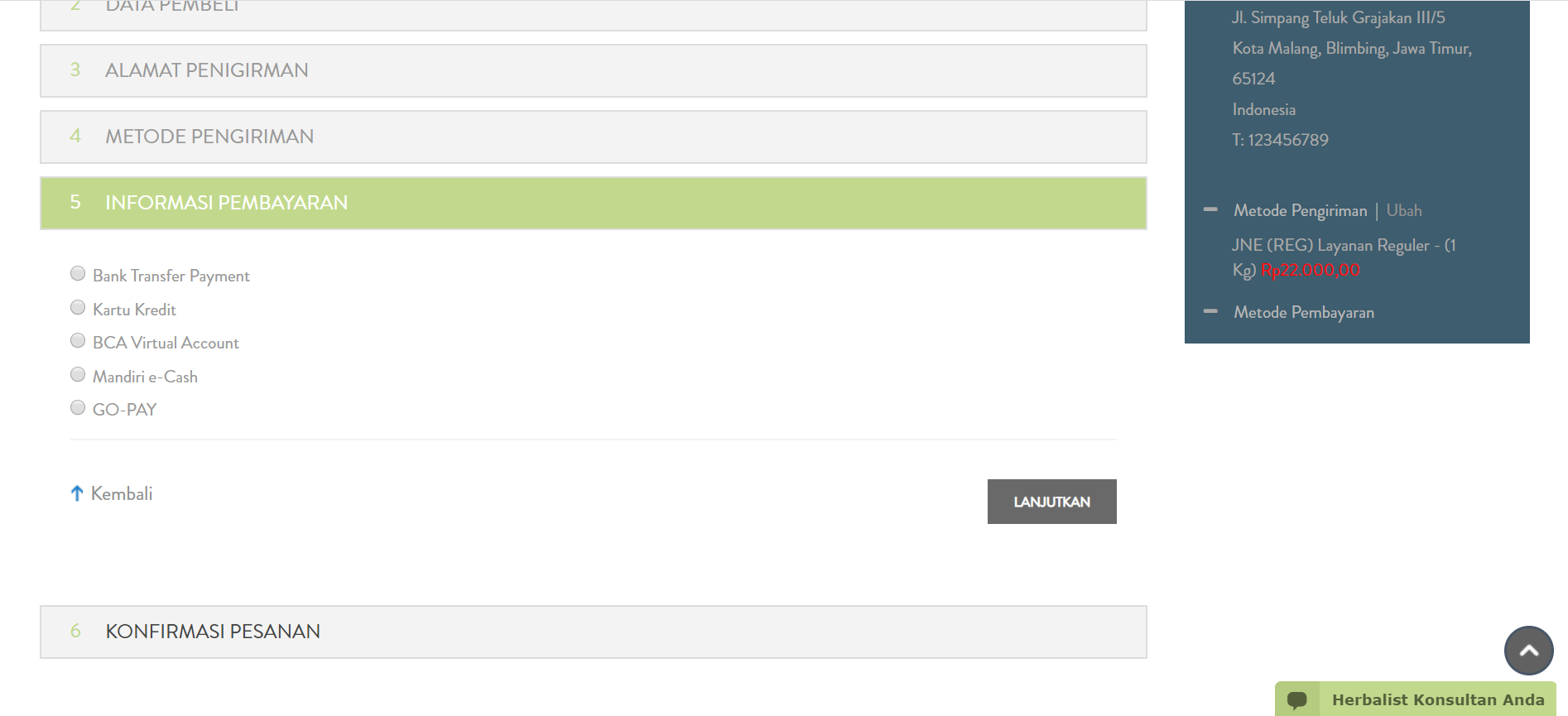
- Midtrans integration is using the standard SNAP integrations. Technically this is pretty smooth as Midtrans already provided a good working module for Magento 1. However, a snag happened because one of the big banks (BCA) took 6 months to approve Mandjur to allow people to pay through BCA. The problem is the people. The solution unfortunately is constantly asking them for updates. But we managed to finally develop the new payment method on the website.
- 6. We also do some general maintenance for the website to make sure it’s working properly, no threats from the attacker, and every user can buy their favorite herbal medicine safely.



accelerating COmmerce, Begin your digital transformation.
Start your project with LimeCommerce
